Temporary Disposal Email Services for Hacking and Security
Tamil Songs | 20:38 |
Corporate Security
,
Email Hacking and Security
Almost every website ask you to Signup for download software, viewing content, online shopping and so on. For example, If once you singup any marketing websites with your real email id, they will send bulk advertisments link dump it in your Inbox. It is not compulsary to every website is trusted. Some Scam Websites can do anything with your email id. So Protect your Real email id from spam. let get ride of this by following steps.
What is Temporary Disposal Email?
Temporary Disposal Email provide random and unique email id for any user (Without Signup) which can be disposed anytime.
Why use Temporary Disposal Email?
* Most Spammer sell email subscription list to marketer which may cause uninterrupted junk spam to our Inbox.
* Read and Receive email instantly with time period
* Avoid Spammer
Step-by-Step Tutorial
Top Temporary Email Service Providers
1. http://10minutemail.com
The below displayed email id is active for next 10 minute.
1. Mailinator:
This is one of the top rated temporary email providers which provides you address of the format something@mailinator.com
2. Yopmail:
Another temporary email address service with good user-friendly email interface. I have tried many services and found yopmail having one of the best interfaces. What more, don't need any cubersome registration process. Simply enter any desired email address and Yopmail has it.
3. Spamgourmet:
This is efficient spam blocker temporary email address service which has also got good reviews elsewhere on web.
4. Jetable:
This is multi-functinal temporary inbox provider which allows you to define time span for which your temporary inbox will be valid. Also, you can forward the temporary inbox mails to your real email address.
5. Spambox:
One of the best feature of this service is time span of disposable email address can be as long as 1 year. This is really a large span. It provides all other features for temporary email address.
6. Mailexpire:
Create an alias email address for your real email address. Mailexpire provides you temporary email address for as long as 3 months. If you want to delete alias mail id instantly, you are always provided with a link to delete your alias temporary disposable email address.
Hope This Tutorial will helpful to you. Leave your comments..
Bypass Phone and SMS verification of Any Website
Tamil Songs | 06:22 |
Bypass SMS AND Mobile verfication
,
Gmail SMS Bypass
Now a days, almost more websites need sms verification which includes google, facebook, youtube and other survey websites.
First of all we should understand why SMS and Phone Verification System?
* Keep More Visitors for Market
* Providing Extra Security for their Website
* Keep Spammers out
* Daily Advertisement and promotional ads daily
2) Copy any one number and paste it where they are asking SMS Verification.
* Keep Spammers out
* Daily Advertisement and promotional ads daily
Rather we can able to create and Bypass gmail (facebook, youtube, other shopping sites) without SMS verification. Because gmail allow to create only few account. When you try to create more account with same mobile number, google restricted and you can't create more account. so we can create counterless gmail accounts using following steps.
This method is very useful to Bypass SMS verification and useful when you need to Sign up any account and do not feel comfortable to giving your real number or if you want to create multiple account.
Lets Start Step by Step:
1) First go to this Website : http://receive-sms-online.com/2) Copy any one number and paste it where they are asking SMS Verification.
3) Simply come back and click the number which you have selected, check it out there is your code sent by google, youtube or whatever else.
Hope You Enjoyed this and leave your comments.
Cracking WEP networks on Windows | WIFI Hacking
Tamil Songs | 20:36 |
The word WEP stands for Wired Equivalent Privacy and this protocols are most commonly used for ensure the wifi but it is most vulnerable and easy to crack. As far as my friends are working as various companies and studying different colleges, the only despite is that they cannot access their nearest WIFI. This Tutorial will helpful to crack wep keys easy methods on Windows. This tutorial is dedicated to one of my friend prabhu who where working in wipro | Hacking Track click aond.
Tools needed
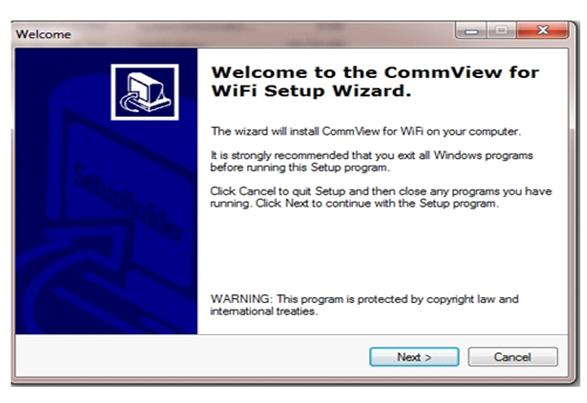
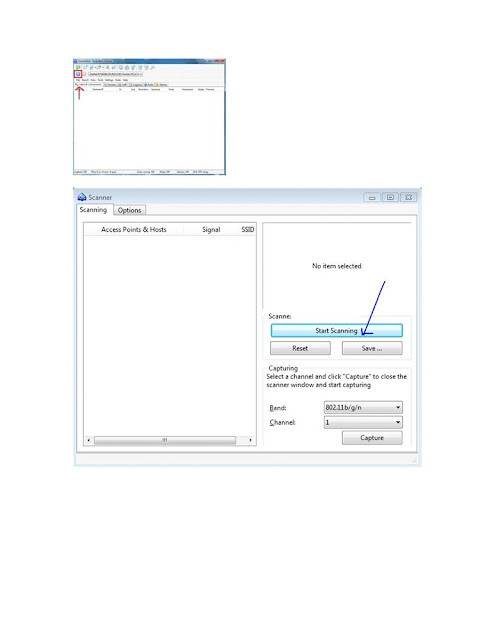
1. Commview for Wifi (Tracking wifi access point and capture the packets)
2. Aircrack-ng (Revealing the password from the packets which is captured by commview)
2. Aircrack-ng (Revealing the password from the packets which is captured by commview)
Steps 1:
Download and Install commview software the link has given above.
Hacking HTML Website using HTML extraction through Google
Tamil Songs | 23:31 |
website hacking
According to my one of the reader request i have posted.
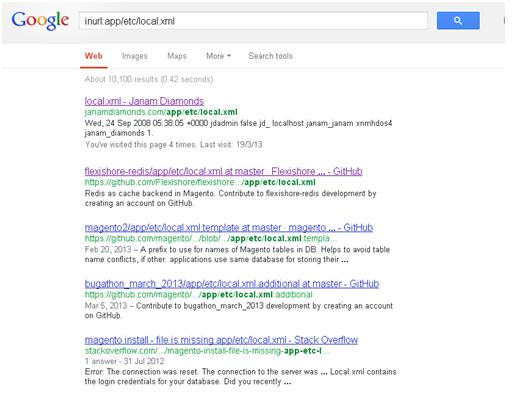
If you are familiar with hacking concept, you should understand that hacking of HTML website is much difficult as far as hacking is concerned, Hacking of HTML simple website is more difficult compared than php, asp.net.HTML sites mostly do not support SQL and Oracle as backend but use XML as the backent. Mostly the username and password are kept in the file called local.xml. Now am show you how HTML website are compromised.
For that we need to use the Google dork "inurl:app/etc/local.xml".
Go to goole search and type "inurl:app/etc/local.xml' and click any one of the links that follow.
from the image that follows, you can see that we got the username and password of the website which is vulnerable to the above HTML extraction exploit
Please leave the comments
Man In The Middle Attack (Session Hijacking Basic)
Tamil Songs | 04:46 |
Email Hacking and Security
Helo folks, Today am gonna show you how does the man in
middle attack works which is also called as Network Hacking.
From this attack you can
compromise victim machine & Hack facebook, gmail etc password and what ever
so on through online session even on Https that is ssl encryption.
Man in the middle attack, is when a attacker sits in the
middle of a network and captures all the packets transferred between two
computers. Attackers position themselves between two systems and actively
participate in the connection to gather data.
Lets take an example, User on a local area network or wifi
and connects to a website called ICICIBANK.COM,
When userpc tries to connect to Bankwebsite, userpc sends a
request to bankserver, This requests are sent in form of data packets, now if
an attacker is carrying out MITm attack,
this packets are being captured again and again by hacker'pc. Thats how
MIMTM attack is carried out. It is carried out by Poisoning the Address
Resolution Protocol(ARP) of a system.
ARP Poisoning:
Address Resolution Protocol spoofing(make identity), also known as ARP
flooding, ARP posoning OR ARPpoison routing, is a technique used to attack an
Ethernet wired or wireless network,. ARP Spoofing may allow an attacker to
sniff data frames on a local area network (LAN)
There are different methods and tools are used. Essential
Technique are given as following.
Fake Email:Send email with any email ID's
Tamil Songs | 20:23 |
Email Hacking and Security
Hey guys, today am gonna teach you how to send fake email to fool your friend or anybody....
In this tutorial i had took revenge to fool my best friends with billgates email id to offering job.
we can also use this fake mail technique for phishing to make mailer appear as genuine.
It is easy to do...let's start....
1.Go to this website http://emkei.cz/

In this tutorial i had took revenge to fool my best friends with billgates email id to offering job.
we can also use this fake mail technique for phishing to make mailer appear as genuine.
It is easy to do...let's start....
1.Go to this website http://emkei.cz/

2. Now enter name whatever you want....i was used bill gates
From Name : Billgates
From E-mail : billgates@microsoft.com
To : your friend email
Subject : offering job
3. Now enter the captcha and hit send
your friend will receive email like this
I guess this fake mailer is easy to use.if you have any problem to send fake mail means right your comment below....
Enjoy fake mail...
Don't forget to leave your comment....